Protecting Data in Transit: Essential Tips for Secure Information Transfer
In today's digital age, protecting data in transit has become a top priority for individuals and businesses alike. Sensitive information is exchanged through various channels every day, from online transactions to emails and instant messages. However, this increased connectivity also exposes data to various threats, making it crucial to implement effective measures to safeguard data during transmission.
Understanding Data in Transit
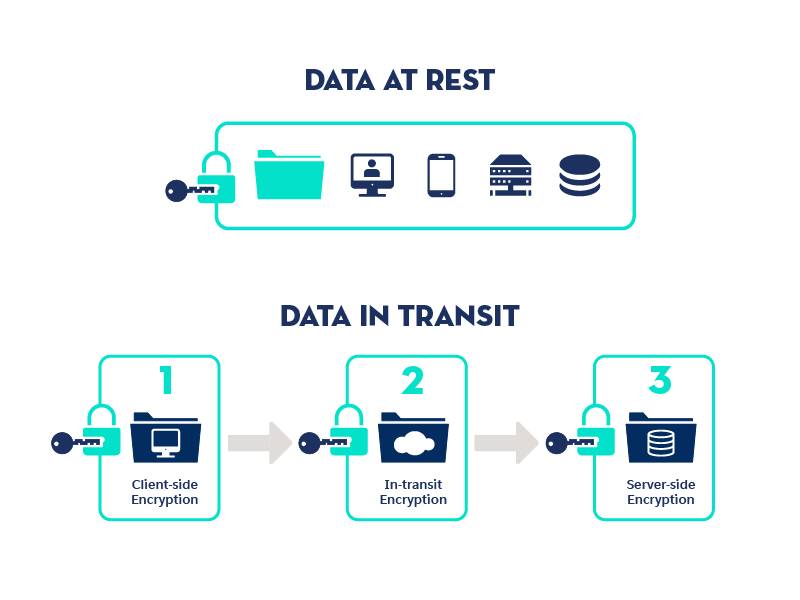
When data is transmitted over a network, it is said to be in transit. This can happen through various means, such as when you send an email, upload a file to the cloud, or make an online payment. Data in transit is vulnerable to interception, manipulation, and unauthorized access, making it essential to implement robust security measures to protect it.
Why Protect Data in Transit?
Protecting data in transit is critical to prevent potential data breaches and maintain confidentiality, integrity, and authenticity. According to Thales Group, 21% to 60% of organizations store sensitive data in the cloud, and 45% of companies have experienced a cloud-based data breach. This highlights the need for robust data protection during transmission.
Top Tips for Protecting Data in Transit

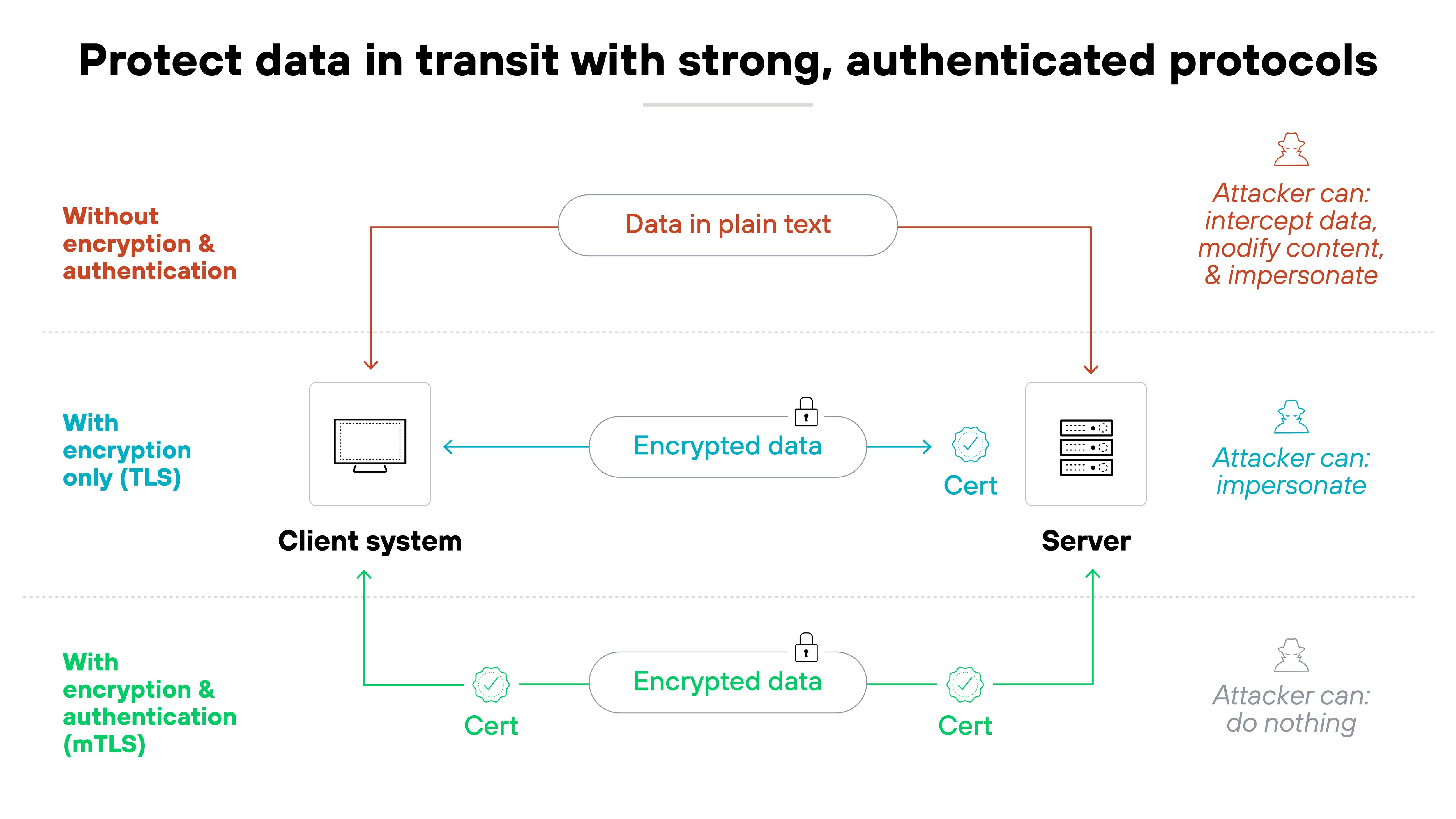
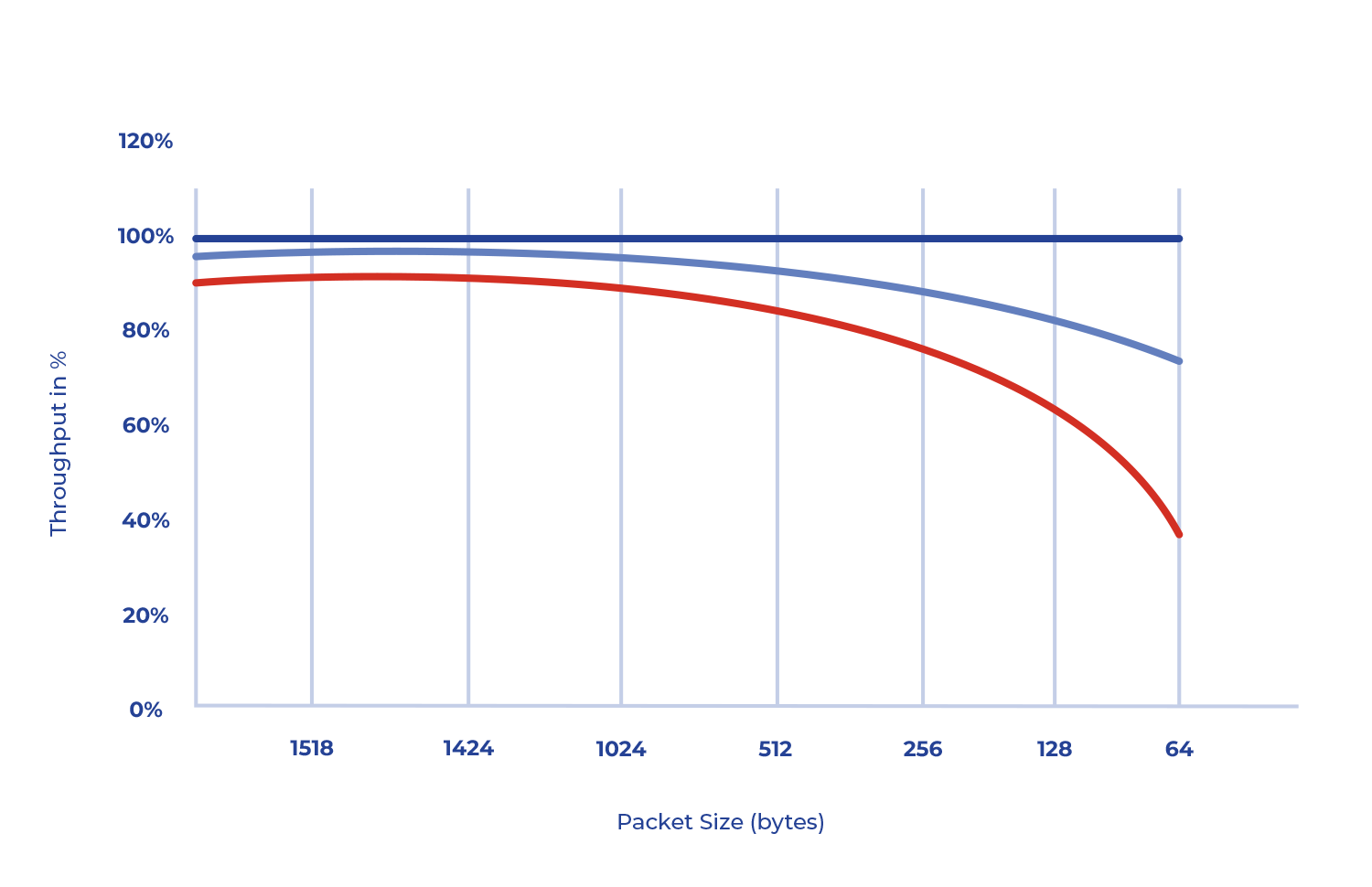
- Implement Encryption Protocols - Encryption is a widely recognized method to protect data in transit. Use secure protocols like TLS (Transport Layer Security), SFTP (Secure File Transfer Protocol), and HTTPS (Hypertext Transfer Protocol Secure) to encode data and prevent unauthorized access.
- Use Secure Network Connections - Ensure that your network connection is secure, using Virtual Private Networks (VPNs) or firewalls to prevent unauthorized access to your data in transit.
- Regularly Update Software and Security Patches - Keep your software and security patches up-to-date to prevent exploitation of vulnerabilities that can compromise your data in transit.
- Conduct Regular Security Audits - Perform regular security audits to identify potential vulnerabilities and take corrective measures to protect data in transit.
- Educate Employees and Stakeholders - Train employees and stakeholders to handle sensitive data securely and be aware of potential threats to prevent data breaches.
- Implement Data Loss Prevention (DLP) Policies - Develop and enforce DLP policies to prevent unauthorized access, leakage, or theft of data during transmission.
- Use Secure Authentication and Authorization - Implement secure authentication and authorization mechanisms to prevent unauthorized access to data in transit.
- Monitor Network Traffic - Regularly monitor network traffic to detect potential threats and take action to prevent data breaches.
- Comply with Regulatory Requirements - Ensure compliance with relevant regulatory requirements, such as GDPR and HIPAA, to protect sensitive data in transit.
Conclusion
Protecting data in transit is crucial to maintain confidentiality, integrity, and authenticity. By implementing the tips outlined above, you can significantly reduce the risk of data breaches and maintain the trust of your customers, partners, and stakeholders. Remember, data in transit is vulnerable to various threats, and robust security measures are essential to safeguard sensitive information.
Final Thoughts
Securing data in transit is an ongoing process that requires continuous monitoring, evaluation, and improvement. By staying informed about the latest security threats and implementing effective security measures, you can protect your data and maintain a secure digital ecosystem. Remember, a proactive approach to data protection is key to ensuring the security of your sensitive information in transit.