Protecting Data from Encryption Attacks: A Comprehensive Guide
In today's digital landscape, data breaches and cyber threats continue to rise at an alarming rate. With organizations of all sizes finding themselves vulnerable to increasingly sophisticated attacks, implementing robust encryption is no longer just about regulatory compliance – it's a necessity. In this article, we will delve into the world of protecting data from encryption attacks, exploring the best practices, tools, and strategies to safeguard your sensitive information.
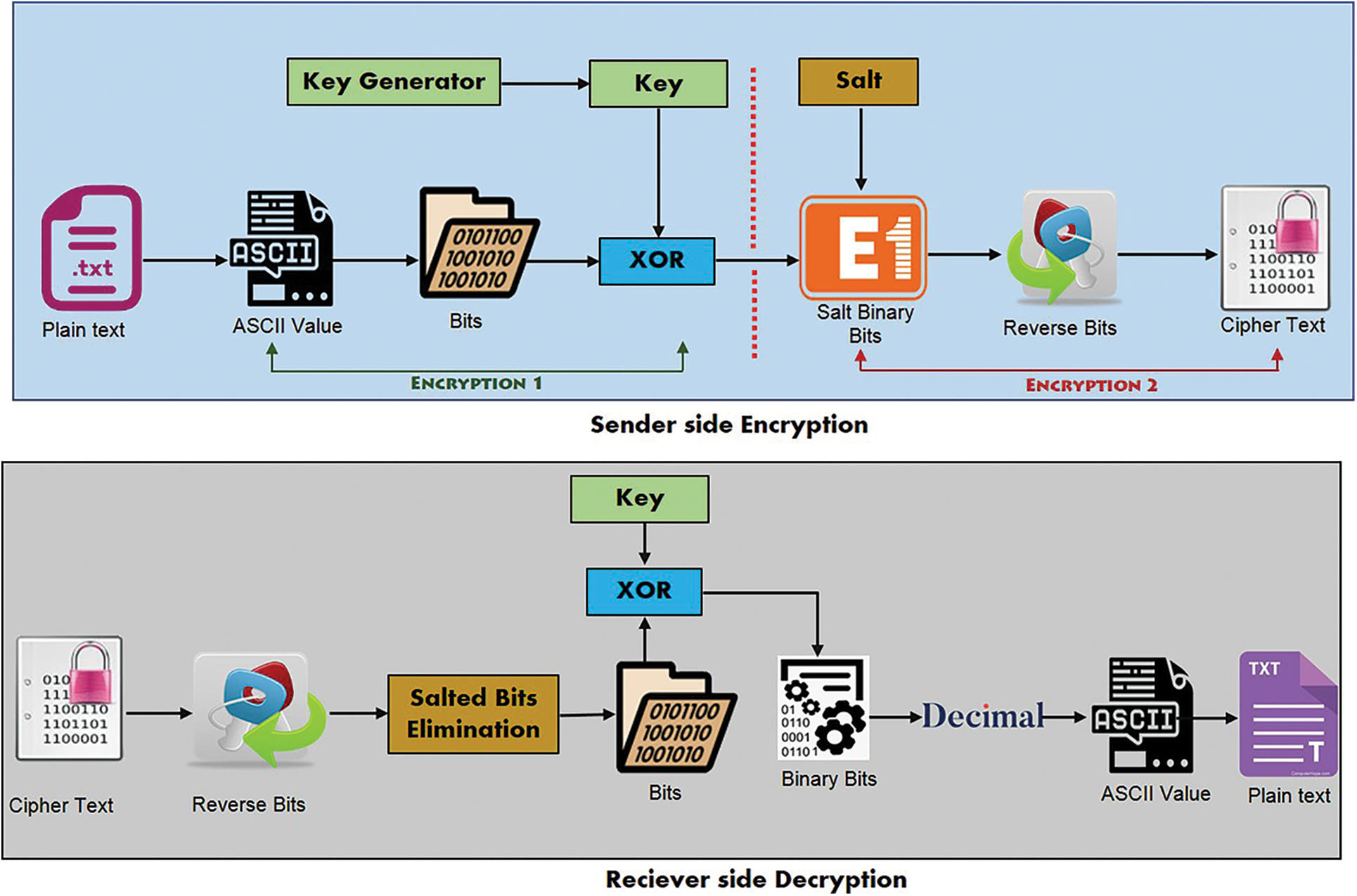
Understanding Encryption and Data Protection
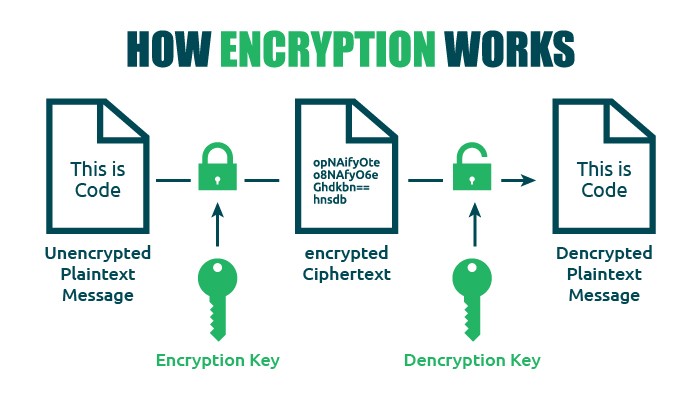
Encryption is a powerful tool in the cybersecurity arsenal, safeguarding data from breaches, cyber threats, and unauthorized access. By converting readable messages into unreadable ciphertext, encryption ensures that even if an encrypted email or file falls into the wrong hands, the sensitive information it contains will remain secure. However, with the increasing complexity of cyber threats, it's essential to understand the limitations of encryption and the various types of attacks that can compromise its effectiveness.
The Anatomy of Encryption Attacks
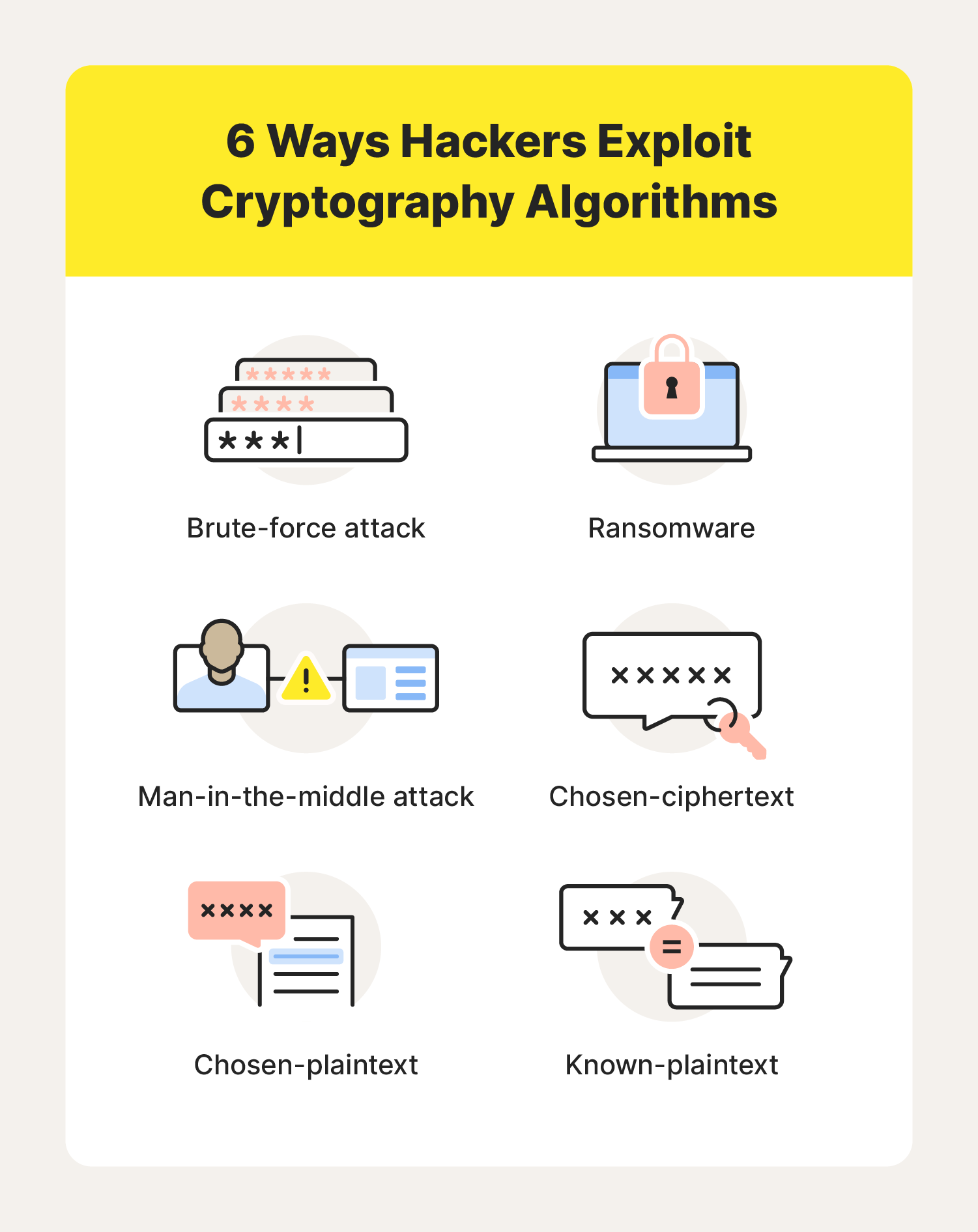
Encryption attacks can take many forms, including brute-force attempts to guess keys, mathematical analysis of encryption algorithms, and exploitation of software vulnerabilities. Modern encryption uses extremely long keys, making brute-force attacks impractical. However, attackers can still use sophisticated techniques to compromise encryption, such as exploiting vulnerabilities in encryption software or using malware to steal encryption keys.
- Brute-force attacks: attackers attempt to guess the encryption key through trial and error
- Mathematical analysis: attackers use mathematical techniques to crack the encryption algorithm
- Software vulnerabilities: attackers exploit vulnerabilities in encryption software to gain access to encrypted data
- Malware: attackers use malware to steal encryption keys or compromise encryption software
Protecting Data from Encryption Attacks
To protect your data from encryption attacks, it's essential to implement a comprehensive security strategy that includes:
- Strong encryption: use advanced encryption algorithms and keys to secure sensitive data
- Key management: securely manage encryption keys to prevent unauthorized access
- Access control: implement robust access controls to restrict access to encrypted data
- Monitoring and detection: continuously monitor and detect potential encryption attacks
- Incident response: have a plan in place to respond to encryption attacks and minimize data loss
Best Practices for Protecting Data from Encryption Attacks
To stay ahead of encryption attacks, it's essential to follow best practices, including:
- Implementing robust encryption protocols, such as TLS and AES
- Using secure key management practices, such as key rotation and escrow
- Regularly updating and patching encryption software and systems
- Monitoring and analyzing encryption logs and system activity
- Conducting regular security audits and penetration testing
Conclusion
Protecting data from encryption attacks requires a comprehensive security strategy that includes strong encryption, key management, access control, monitoring, and incident response. By understanding the anatomy of encryption attacks and implementing best practices, organizations can safeguard their sensitive information and minimize the risk of data breaches and cyber threats. Remember, protecting data from encryption attacks is an ongoing process that requires continuous monitoring, detection, and response.
Additional Resources
For more information on protecting data from encryption attacks, check out the following resources:
- CISA (Cybersecurity and Infrastructure Security Agency) guidelines for encrypting data
- Fortra's data loss prevention (DLP) software for discovering, monitoring, and blocking sensitive data
- Sophos Endpoint's CryptoGuard technology for monitoring and blocking malicious encryption
- HP's TPM Guard for protecting against physical access attacks