Cloud Security Against Phishing Threats: Protecting Your Organization's Data
Phishing attacks continue to be a significant threat to cloud security, with attackers leveraging various tactics to compromise cloud identities. Despite advancements in protections like multifactor authentication (MFA) and passwordless solutions, social engineering remains a key aspect of phishing attacks. Implementing phishing-resistant solutions, like passkeys, can improve security against these evolving threats.
The Risks of Cloud Phishing
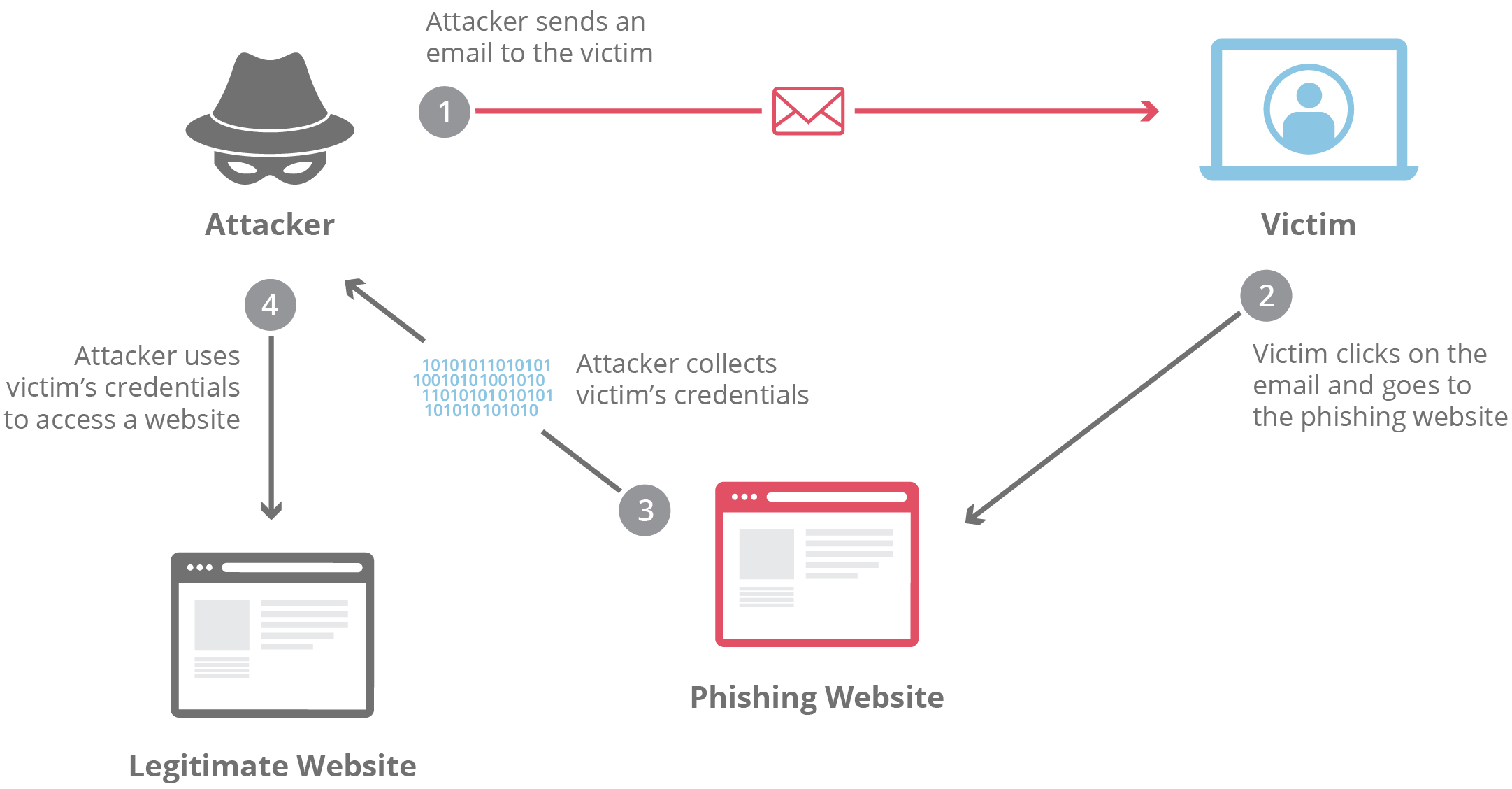
Cloud phishing attacks can have devastating consequences for organizations, including data breaches, financial losses, and damage to reputation. Attackers use various tactics to trick users into revealing sensitive information, such as passwords, account numbers, or social security numbers. If they gain access to this information, they can compromise cloud platforms, gain long-term access without credentials, and even sell the information to other scammers.
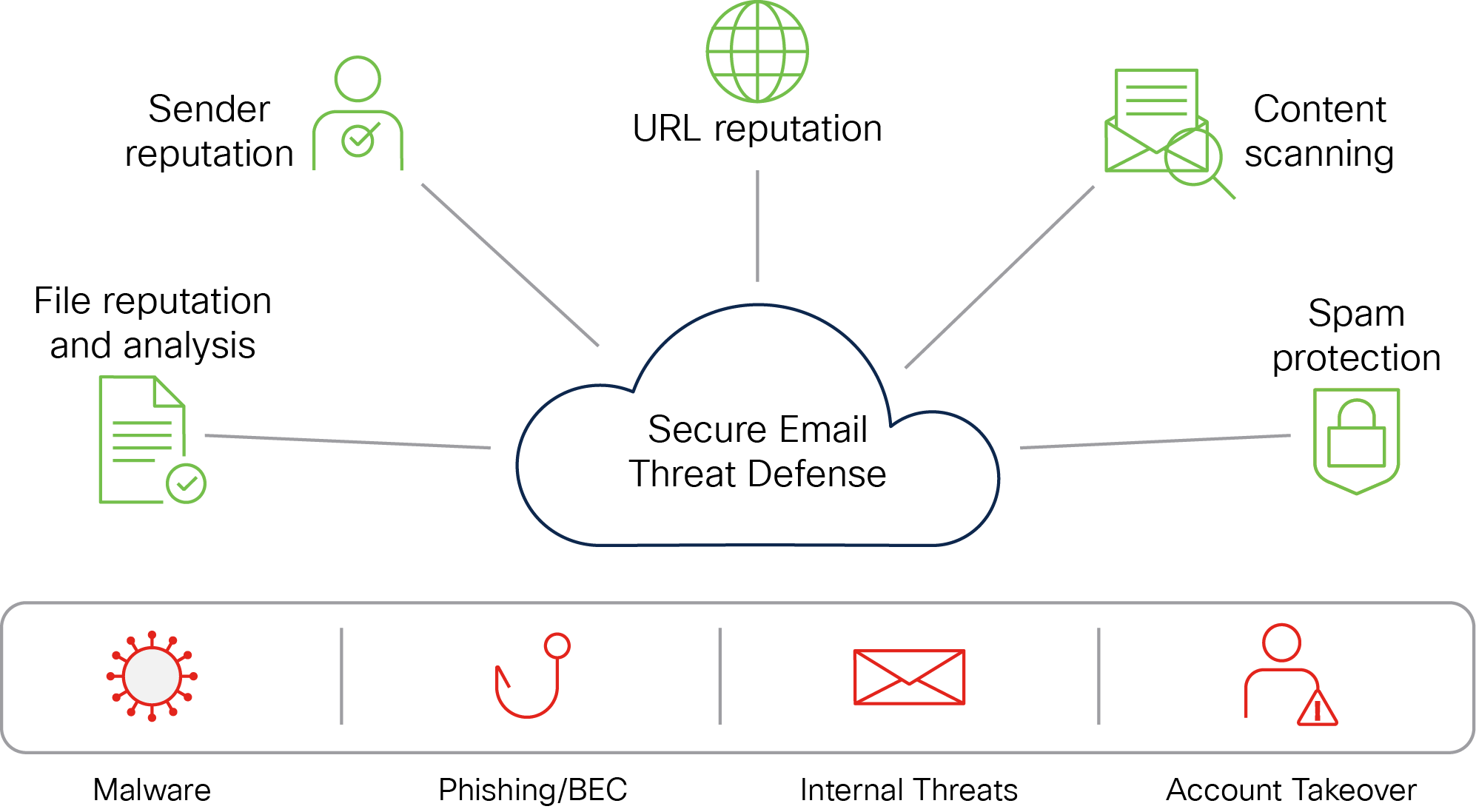
The Importance of Cloud Security Against Phishing Threats
Cloud security against phishing threats is essential to protect organizations from these types of attacks. Implementing a combination of security measures, such as AI-driven analysis, automated workflows, and robust security policies, can help detect and respond to phishing threats targeting cloud environments. This can include using advanced email protection to prevent credential phishing, business email compromise, account takeover, and more.
Tools and Solutions to Combat Cloud Phishing
Several tools and solutions can help organizations combat cloud phishing threats, including:

- Cloud-based security information and event management (SIEM) systems to monitor and analyze security-related data
- Cloud access security brokers (CASBs) to detect and block suspicious activity, as well as enforce security policies to prevent data breaches
- Password managers to generate and store unique and complex passwords for every account
- Cloud email security solutions that analyze behavior in real-time using AI, sandboxing, and isolation to detect and prevent unknown threats
- Phishing-awareness training to educate employees on the risks and tactics of phishing attacks
Best Practices for Cloud Security Against Phishing Threats
To protect against phishing threats, organizations should follow best practices, including:
- Implementing MFA and passwordless solutions to reduce the risk of password-based attacks
- Using AI-driven analysis and automated workflows to detect and respond to phishing threats
- Enforcing robust security policies to prevent data breaches and unauthorized access
- Providing regular training and awareness programs for employees on phishing risks and tactics
- Regularly updating software and systems to prevent exploitation of known vulnerabilities
Conclusion
Cloud security against phishing threats is a critical aspect of protecting organizations from data breaches, financial losses, and damage to reputation. By implementing a combination of security measures, including AI-driven analysis, automated workflows, and robust security policies, organizations can detect and respond to phishing threats targeting cloud environments. By following best practices and staying informed about the latest cloud security threats, organizations can stay ahead of phishing attacks and protect their data in the cloud.