Risks in Modern Pc Hardware Setup: A Comprehensive Guide
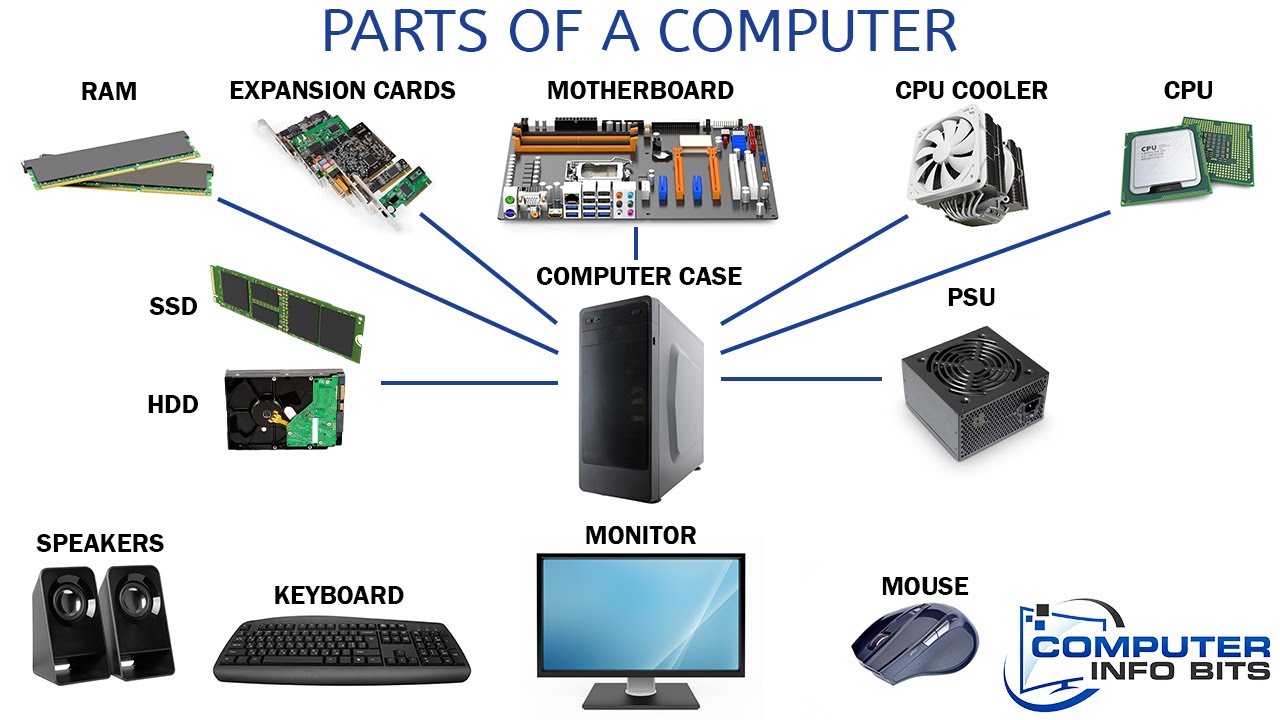
Modern PC hardware setup has become increasingly complex, with the integration of various components and technologies. However, this complexity has also introduced new risks and vulnerabilities that can compromise the security and integrity of your system. In this article, we will explore the risks associated with modern PC hardware setup and provide guidance on how to mitigate these risks.
Hardware Vulnerabilities
Hardware vulnerabilities refer to weaknesses in the design, manufacturing, or assembly of computer hardware that can be exploited by attackers to gain unauthorized access to a system. These vulnerabilities can be introduced during the design stage, fabrication, or assembly and testing phases of the hardware manufacturing process. As modern chips contain billions of transistor components, the risk of hardware vulnerabilities is high, making it challenging to detect and fix them.
Common Hardware Vulnerabilities
- Intel and AMD chip vulnerabilities: Meltdown and Specter affected most modern computers, including Intel, AMD, and smartphones. To mitigate these risks, keep your operating system and CPU microcode up-to-date.
- Firmware vulnerabilities: Firmware is software but is closely tied to hardware. Outdated firmware can expose systems to security risks, and regular updates are essential to stay protected.
- Hardware security vulnerabilities: Exploiting hardware vulnerabilities can be more complex than software vulnerabilities, but they can be just as detrimental. A secure Pluton chip, designed by Microsoft, provides an additional layer of security against hardware attacks.
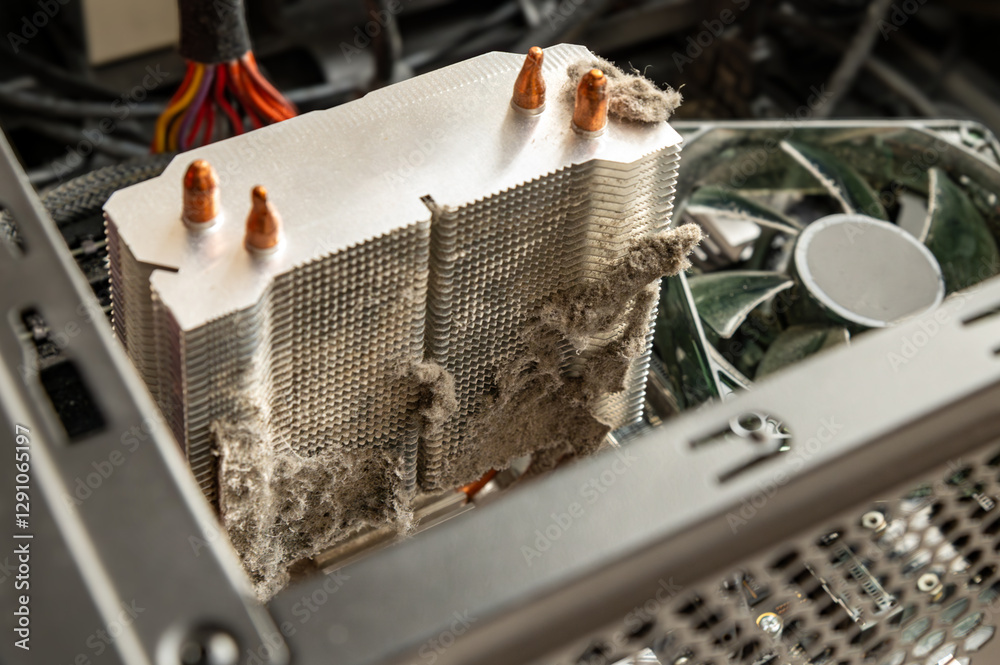
Risks of DIY Computer Hardware Installation and Upgrades
Installing or upgrading computer hardware without professional help can be fraught with risks. Damaging components, voiding warranties, and wasting time and money are some of the potential pitfalls. Proper safety precautions, such as wearing protective clothing, unplugging equipment before opening cases, and following proper installation procedures, can minimize these risks.

Importance of Hardware Security and Risk Assessment
Hardware security has evolved into a pressing IT issue as enterprises incorporate autonomous sensors, controllers, and monitors into their smart buildings and IoT projects. Conducting rigorous risk assessments is essential to identify and mitigate potential hardware-related threats. Merging traditional risk assessment practices with modern data analytics will help hardware engineers develop more robust and secure products.
Best Practices for Minimizing Risks in Modern PC Hardware Setup
To minimize the risks associated with modern PC hardware setup, follow these best practices:
- Keep your operating system and CPU microcode up-to-date.
- Regularly update firmware to address potential vulnerabilities.
- Invest in up-to-date hardware to ensure compatibility and security.
- Dispose of outdated hardware securely to prevent data breaches.
Conclusion
Modern PC hardware setup presents a range of risks and vulnerabilities that can compromise system security and integrity. By understanding these risks and following best practices, you can minimize the potential dangers associated with modern PC hardware setup. Remember to keep your operating system and CPU microcode up-to-date, regularly update firmware, conduct rigorous risk assessments, and invest in up-to-date hardware to ensure a secure and reliable system.







![Download Windows XP ISO Files [32-Bit & 64-Bit]: Direct Links Download Windows XP ISO Files [32-Bit & 64-Bit]: Direct Links](https://www.hardwarejournal.co.nz/wp-content/uploads/2024/03/Hardware-Virtualization.jpg)