Best Online Security Practices for Non-Profits
Cybersecurity is a crucial aspect of every organization, and non-profits are no exception. In today's digital age, the importance of cybersecurity for non-profits cannot be overstated. Non-profit organizations often handle sensitive information, including donor data, financial records, and personal details of beneficiaries, making them attractive targets for cybercriminals who seek to exploit vulnerabilities for financial gain or to disrupt operations. In this article, we will delve into the best online security practices for non-profits, ensuring the protection of sensitive data and maintaining donor trust.
Understanding Your Organization's Risks
Before you can protect your organization, you need to understand the cybersecurity risks you face. Take inventory of all the data you collect and identify where it is stored to begin assessing your organization's data risks. Ask yourself, "What data do we collect about people?" Be sure to consider both internal data, such as employee information, and external data, like donor and beneficiary information.
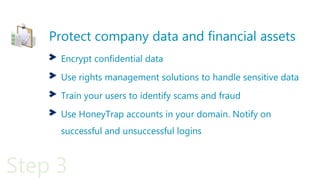
Implementing Security Measures
- Conduct regular risk assessments and vulnerability testing to identify potential security breaches.
- Certify all employees, especially those with sensitive access, on cybersecurity best practices and data protection.
- Use reputable antivirus software and maintain up-to-date software to prevent malware and virus infections.
- Implement a secure password policy and use multi-factor authentication to secure access to sensitive data.
- Regularly back up sensitive data and ensure backups are stored securely.
- Utilize spam and phishing filters to protect against email-based threats.
- Be cautious when using public Wi-Fi and protect your devices with virtual private networks (VPNs).
Creating a Cybersecurity Policy
A comprehensive cybersecurity policy should address donor privacy, financial compliance, and volunteer access management. This policy should be a guiding document for all employees, including directors, executives, and volunteers. By implementing a clear policy, your non-profit demonstrates a commitment to protecting sensitive data and maintaining the trust of donors and stakeholders.

Continuity and Preparation
Although cybersecurity risks cannot be completely eliminated, having a plan in place can help your organization respond to and recover from a security breach. Consider how a breach would impact your operations, donors, and stakeholders. Develop a plan to recover from a breach, and make sure it includes measures for damage control, communication, and restoration of services.
Partnerships and Training
Non-profits can rely on the voluminous guidance and best practices found in the business world, regulatory guidelines, and international standards to perform risk analyses, conduct internal assessments, effectively allocate resources, and formulate sound long-term security strategies. State associations of non-profits may offer special workshops or educational programs on cybersecurity, and organizations can seek out partnerships with security experts to help them stay informed and up-to-date on the latest best practices.
Conclusion
Protecting sensitive data and minimizing the risks of a cyber breach should be a top priority for non-profits. By understanding your organization's risks, implementing security measures, creating a comprehensive cybersecurity policy, and ensuring continuity and preparation, your organization can protect itself against cyber threats and maintain the trust of donors and stakeholders. Defense requires continuous investment in education, security sophistication, and resources. In this age of unlimited accessibility and endless digital connections, prepare to address your non-profit's security threats head-on.