How to Protect Instagram from Being Hacked: Essential Security Tips and Best Practices



ProtectyourInstagramfromhackers with strong passwords and MFA. Learn tips to secure your account andhowtotell if your account has beenhacked.

Aug 7, 2025Worried about yourInstagramhackedaccount? Learnhowtoprevent attacks,protectit, and recover it fast with expert steps from Bitdefender.
Get help withhackedInstagramaccounts: Find outhowtorecover ahackedaccount, what to do to secure your account from hackers and phishing attempts.

Get help recovering and securing yourInstagramaccount if it has beenhacked.

May 31, 2024Worried that someone knowshowtohack into yourInstagram? Here'showthey could do it, andhowtoprevent it.

Jun 24, 2025Discover 4 important strategies toprotectyourInstagramaccount from beinghacked, as well as what to do if your account is compromised.
Dec 3, 2025Learn 8 essential ways to preventInstagramhacking: strong passwords, 2FA, login alerts, and account monitoring.Protectyour account today with proven security strategies.

Oct 30, 2024Protecting yourInstagrambusiness account is crucial to maintaining your brand's reputation and preventing personal information theft. In this guide, we'll talk through the best practices allInstagramaccount owners should follow toprotecttheirInstagramaccounts.HowtoprotectyourInstagramfrombeinghacked

Dec 25, 2025Worried about yourInstagramgettinghacked?ProtectyourInstagramfromhackers with this essential security checklist. Secure yourInstagramlike a pro with this in-depth checklist.

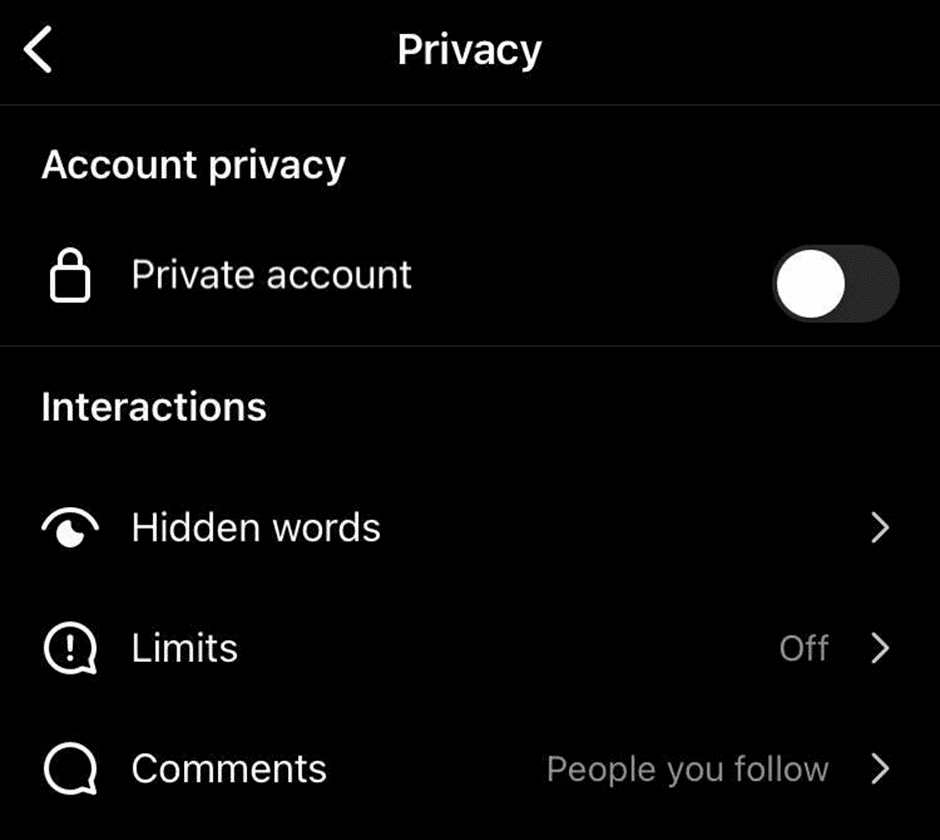
6 tips onhowtoprotectyourInstagramaccount from hackers Nothing can 100% guarantee preventing anInstagramaccount from gettinghacked, but there are things that will definitely reduce the risk. Follow the recommendations below toprotectyour data from hackers.
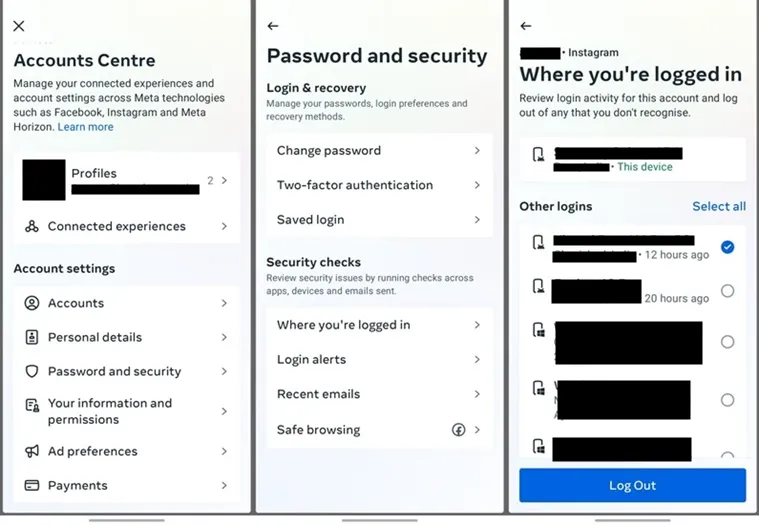
If your account washackedor compromised, you can take action to regain your account. Visit the Facebook Help Center or theInstagramHelp Center to learnhowtosecure your account. We'll ask you to change your password and review recent login activity.
ProtectyourInstagramaccount today — before it'shacked🔐 Most people act after losing access. Smart creators and businesses secure their accounts before problems start. A few simple settings canprotectyour data, followers, and brand reputation. Don't wait for a warning fromInstagram— take control now.Instagramaccount security,protectInstagramaccount,Instagramhacked...

ProtectyourInstagramaccount today — before it'shacked🔐 Most people act after losing access. Smart creators and businesses secure their accounts before problems start.

ProtectyourInstagramaccount today — before it'shacked🔐 Most people act after losing access. Smart creators and businesses secure their accounts before problems start.

ProtectyourInstagramaccount today — before it'shacked🔐 Most people act after losing access. Smart creators and businesses secure their accounts before problems start. A few simple settings canprotectyour data, followers, and brand reputation. Don't wait for a warning fromInstagram— take control now.Instagramaccount security,protectInstagramaccount,Instagramhacked...
6 days agoA hacking tool called Darksword can steal information off your iPhone. What is it? Andhowcan youprotectyourself from beinghacked.

2 days agoHowcan Iprotectmy businessInstagramfromgettinghackedagain? Use two-factor authentication via an authenticator app, secure your email accounts, review Meta Business Manager admins, remove suspicious linked apps, and implement internal access controls for your team.

I had myInstagramaccounthacked, username, password, mobile and email changed & after 3 hours of messing around I finally figured outhowtoget it back. This process is done via video verification & can allow you to gain access back to your account and reset your password and primary email attached to your account.