Wireless Network Security for Entrepreneurs: Protect Your Business from Cyber Threats
As an entrepreneur, you understand the importance of staying connected and productive on-the-go. Your wireless network is a vital part of your business operations, enabling employees to access critical information and stay connected with clients and partners. However, with the increased use of wireless technology comes the risk of cyber threats and security breaches. In this comprehensive guide, we'll discuss the importance of wireless network security for entrepreneurs and provide essential best practices to protect your business.
Understanding the Risks of Wireless Network Security
Wireless network security refers to the strategies, technologies, and protocols used to protect data as it travels over wireless networks. Without proper security in place, your business becomes an easy target for cybercriminals looking to exploit vulnerabilities in your network. Wireless networks introduce additional security risks, making it crucial to take appropriate precautions to protect your information.
7 Essential Wireless Network Security Best Practices for Entrepreneurs
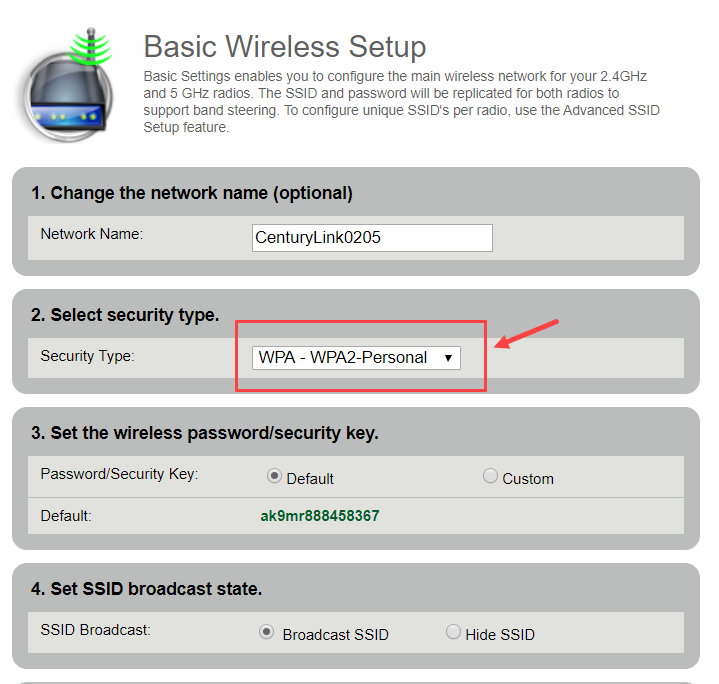
- 1. Use a Strong Password: Change the default password on your router and access point, and use a strong, unique password that includes a mix of letters, numbers, and special characters.
- 2. Enable WPA2 Encryption: Use WPA2 encryption to secure your wireless network and prevent unauthorized access.
- 3. Set Up a VPN: Virtual private networks (VPNs) encrypt data transmitted over the internet, protecting sensitive information from interception.
- 4. Use a Wireless Network Access Control (WNAC) System: Implement a WNAC system to limit access to secure areas of your network and control device authentication.
- 5. Regularly Update Firmware and Software: Keep your router, access point, and other network devices up-to-date with the latest security patches and firmware updates.
- 6. Monitor Your Network: Regularly scan your network for malware and unauthorized access points, and take action promptly to address any security issues.
- 7. Implement a BYOD Policy: Develop a Bring Your Own Device (BYOD) policy to ensure mobile devices accessing your network are properly secured and meet your company's security standards.
The Importance of Centralized Management in Wireless Network Security
Centralized management is critical in wireless network security. A centrally managed WLAN system allows for regular security audits and coordinated updates, ensuring that your network remains secure and up-to-date. Additionally, centralized management enables you to monitor your network, detect potential security threats, and respond promptly to prevent security breaches.
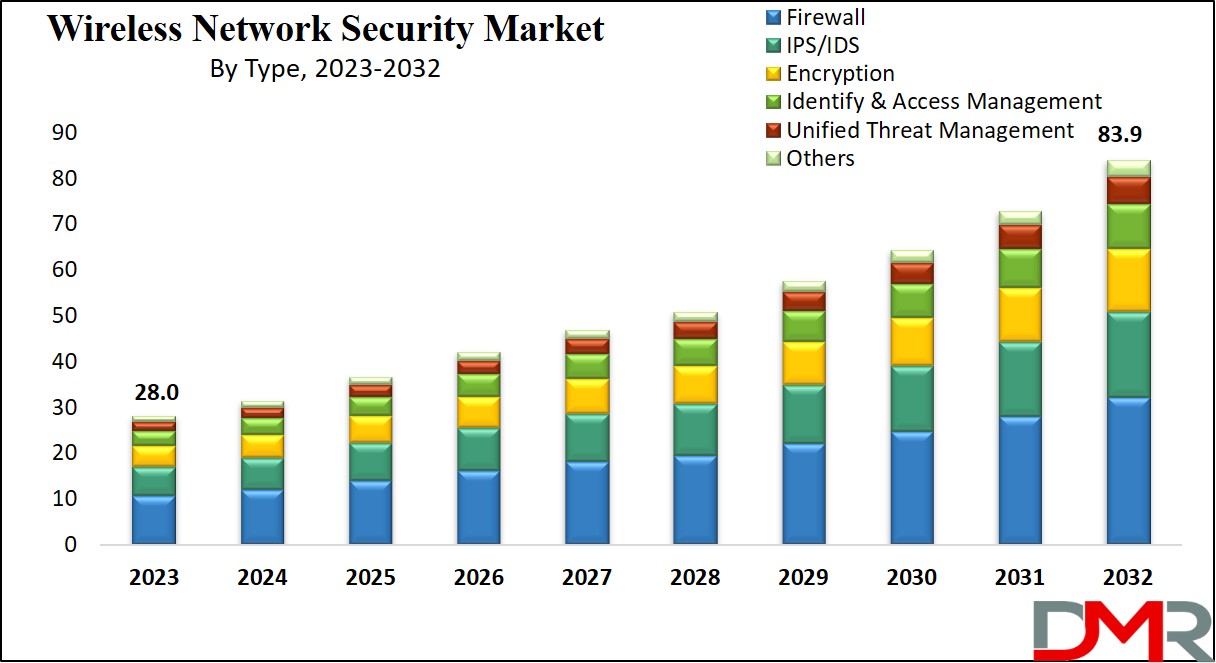
Choosing the Right Network Security Provider
As a small business owner, choosing the right network security provider is crucial to protecting your business. Consider the following characteristics when selecting a provider:
- Experience in Small Business Security: Look for a provider with experience in small business security and a proven track record of protecting businesses like yours.
- Comprehensive Security Solutions: Choose a provider that offers a comprehensive suite of security solutions, including firewalls, antivirus software, and network monitoring.
- Easy-to-Use Interface: Opt for a provider with an easy-to-use interface that simplifies network configuration and security management.
- Support and Training: Select a provider that offers exceptional customer support and training to ensure you're equipped to manage your network security effectively.
Conclusion
Wireless network security is a critical aspect of protecting your business from cyber threats. By understanding the risks associated with wireless networks and implementing essential security best practices, you can safeguard your business from unauthorized access and data breaches. Remember to choose the right network security provider, and stay vigilant in your efforts to protect your wireless network. By taking these proactive steps, you can ensure the security and integrity of your business operations.




![Wireless Security for Small Business: Top Tips [2025] - Network Lab Wireless Security for Small Business: Top Tips [2025] - Network Lab](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEj-c3GkwgXFgQM-YjeShNFLyNcDaG6M8cQVw26sFwXG7vTDYcfAokmKrHN9kMLETOMl335V_xtCxDRJe_KCDPVIZ5SRxQFT9jdi1TBJJp_m_qrevdonjLbdUOa3I3WTb5r95TrWp66ySdsjuUoNY-BONywEhJyE1j8MnaTjkW7nNjBrHwvxp-F7XHHecg/s1920/network%20security%20devices.webp)