Protecting Your Email from Spam and Viruses: A Comprehensive Guide
The Evolving Threat of Email-Borne Malware
Email has become an integral part of our daily lives, serving as a primary means of communication for both personal and professional purposes. However, with its widespread adoption, email has also become a prime target for cyber attackers seeking to exploit vulnerabilities and gain unauthorized access to sensitive information. Spam and virus-infected emails pose a significant threat, showcasing the importance of protecting your email from such malicious activities.Understanding the Risks of Spam and Viruses
Spam emails, often designed to collect sensitive information or deceive recipients into revealing critical data, can be particularly damaging. Equally, malware-laden emails pose a substantial threat, enabling hackers to infiltrate devices and undermine personal and business security. The risk of these threats is especially pronounced for individuals using public Wi-Fi or older systems.Prevention and Protection Strategies
To safeguard your email against the increasing threat of spam and viruses, consider the following strategies: *Utilize Reliable Email Security Software
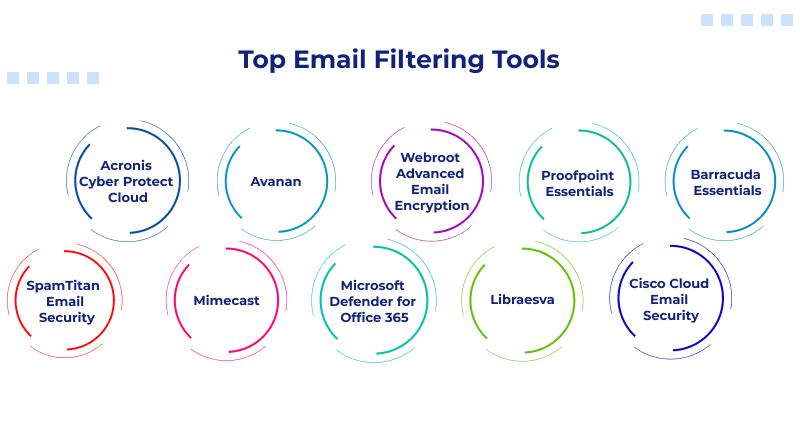
Effectively protect your inbox from spam and viruses by leveraging top-notch email security software. These tools provide comprehensive protection against evolving threats, including phishing, malware, and spam. *Update Your Software Regularly