Protect PC Tools Have Phishing Security
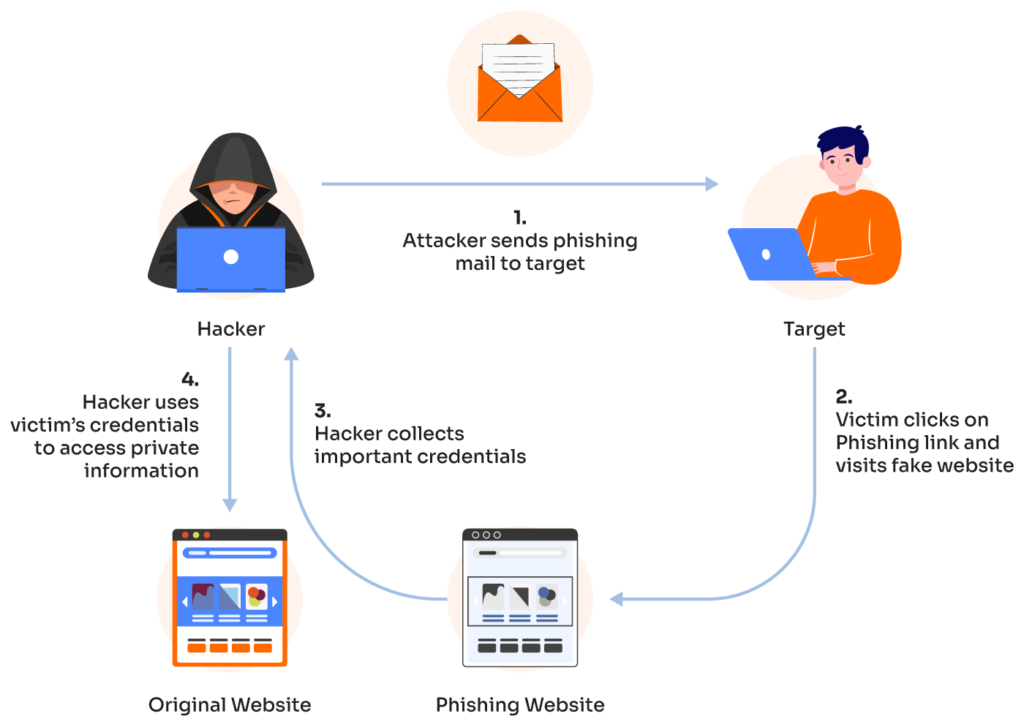
Phishing is a sophisticated cybercrime that involves attackers contacting individuals for their sensitive information to access accounts, steal data, and identities, and download malware onto a user's computer via email, browser, phone, or social media. In this article, we'll explore the importance of protecting PC tools from phishing attacks and how to safeguard your digital life.
What is Phishing?
Phishing is a form of social engineering attack where attackers send fake emails, messages, or pop-ups that appear to be from legitimate sources, such as banks, online retailers, or social media platforms. These messages typically include links or attachments that, when clicked or opened, install malware or steal sensitive information.
Why is Phishing a Threat to PC Tools?
Phishing attacks can compromise PC tools in various ways:
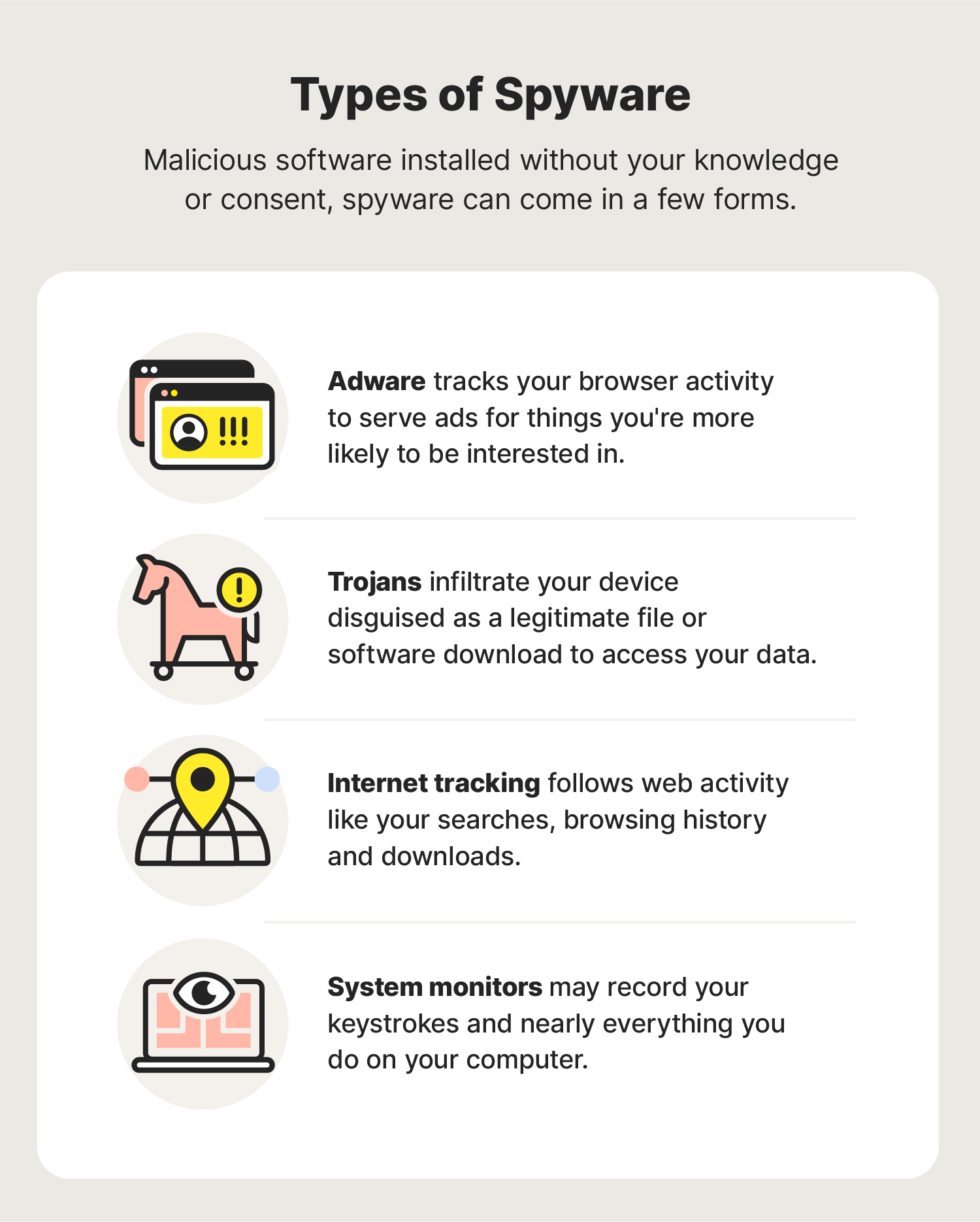
- Malware installation: Phishing attacks can lead to the installation of malware on a user's PC, which can steal sensitive information, compromise passwords, or even take control of the device.
- Sensitive information theft: Phishing attacks can steal sensitive information, such as credit card numbers, login credentials, or personal data, which can be used for identity theft or financial fraud.
- Data breaches: Phishing attacks can lead to data breaches, where sensitive information is exposed, and vulnerable to cyber threats.
Protect PC Tools from Phishing Attacks
To protect PC tools from phishing attacks, follow these best practices:
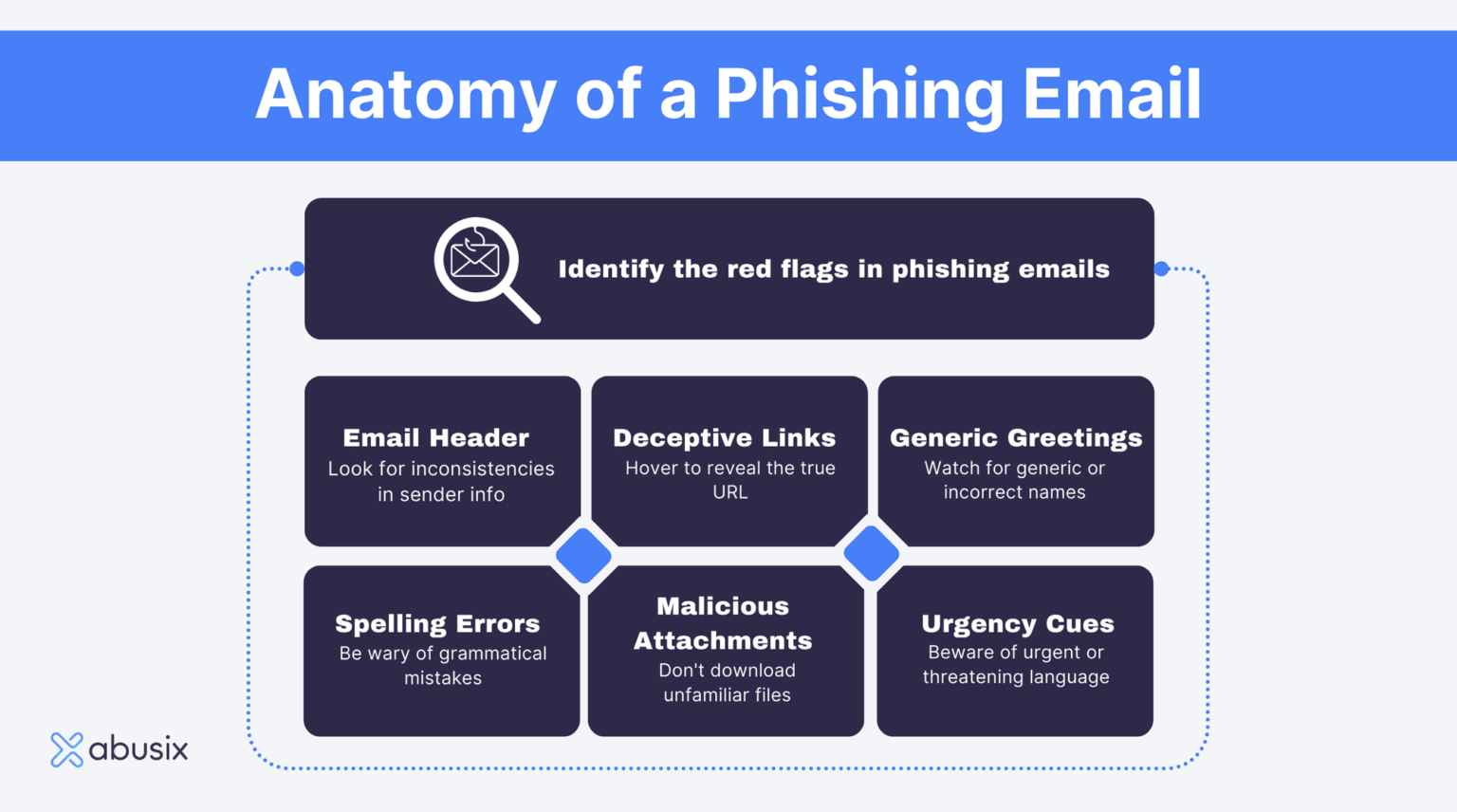
- Exercise caution with emails and messages: Be suspicious of emails and messages that ask for sensitive information, and never click on suspicious links or open attachments from unknown sources.
- Use robust security software: Install reputable security software that includes anti-phishing features to detect and block phishing attacks.
- Enable two-factor authentication (2FA): Enable 2FA for email accounts, social media, and other online services to add an extra layer of security.
- Monitor online accounts: Regularly monitor online accounts for suspicious activity, and report any suspicious activity to the relevant platforms.
- Keep software up-to-date: Regularly update operating systems, browsers, and other software to ensure you have the latest security patches.

The Importance of Phishing Protection Tools
Phishing protection tools are essential for safeguarding PC tools from phishing attacks. These tools can help detect and block phishing attacks in real-time, protecting sensitive information and preventing malware installation. Some popular phishing protection tools include:
- Microsoft Defender Antivirus: Offers robust anti-phishing features to detect and block phishing attacks.
- Avast Antivirus: Detects, blocks, and removes all types of malware, including phishing threats.
- Sophos Endpoint Security: Takes a prevention-first approach to security, blocking ransomware, phishing, and credential-based attacks before they spread.
Conclusion
Phishing is a sophisticated cybercrime that can compromise PC tools and sensitive information. By exercising caution with emails and messages, using robust security software, enabling two-factor authentication, and monitoring online accounts, you can protect PC tools from phishing attacks. Additionally, using phishing protection tools can provide an extra layer of security and safeguard your digital life.
Additional Resources
For more information on phishing and phishing protection, visit the following resources:
- Microsoft Security Research: Analyzes suspicious files to determine if they are threats, unwanted applications, or normal files.
- Avast Antivirus: Provides advanced machine learning techniques to protect against ransomware attacks and other emerging threats.
- CIS Security: Offers a forward-thinking approach to cybersecurity, harnessing the power of a global IT community to safeguard public and private organizations against cyber threats.
Remember, protecting PC tools from phishing attacks is a shared responsibility between individuals and organizations. By working together, we can create a safer digital world and safeguard sensitive information.



![Top 10 Phishing Protection Solutions [2026 RANKINGS] Top 10 Phishing Protection Solutions [2026 RANKINGS]](https://timely-benefit-e63d540317.media.strapiapp.com/Key_Must_Have_Features_of_Anti_Phishing_Software_ffeb822e48.jpg)