IP Address Security Software: A Comprehensive Guide
With the increasing number of cyber threats and data breaches, businesses and individuals need to take proactive measures to protect their online identity and sensitive information. One of the most effective ways to do this is by using IP address security software. In this article, we will explore the importance of IP address security, the types of threats that IP address security software can help protect against, and the top solutions in the market.
What is IP Address Security Software?
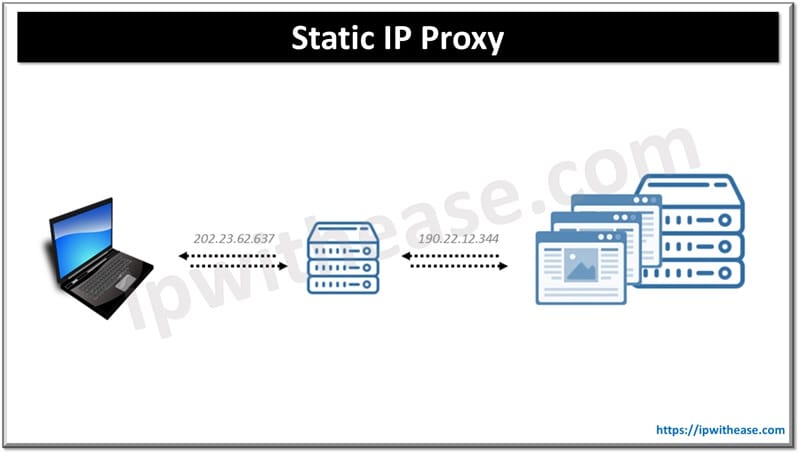
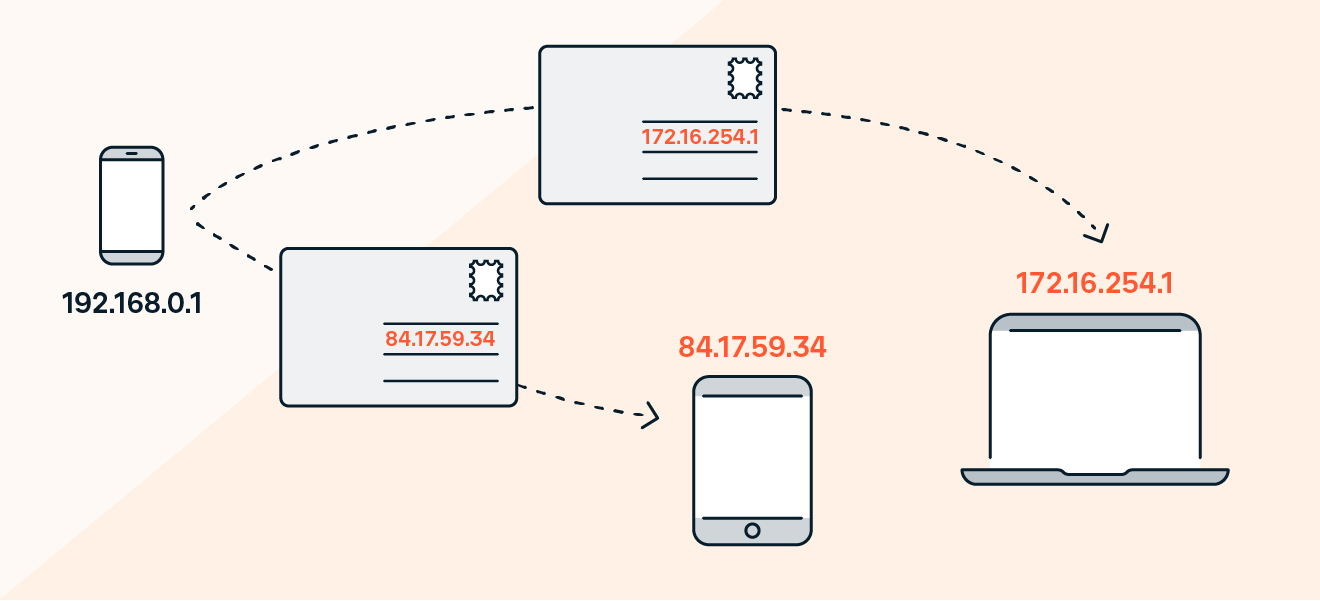
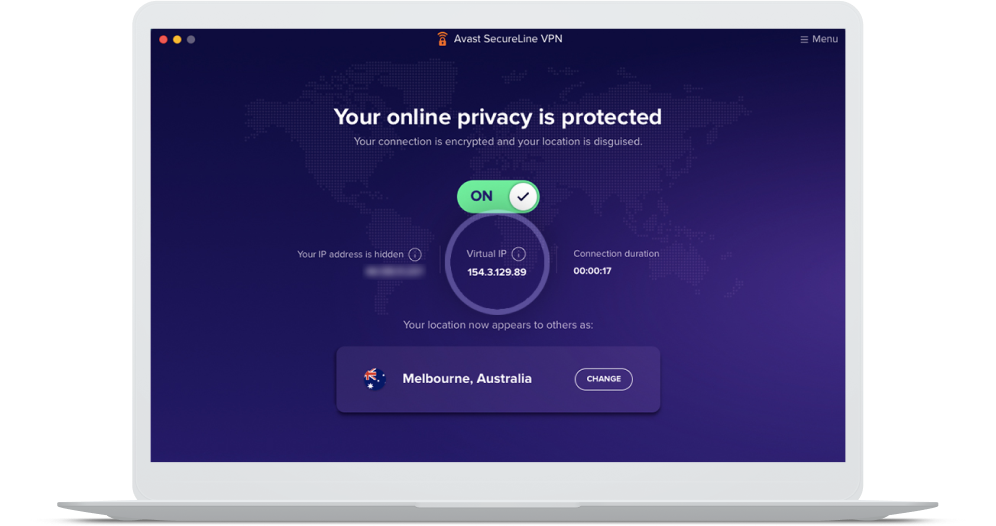
IP address security software is a type of cybersecurity software that helps protect IP addresses from unauthorized access, hacking, and other types of cyber threats. It works by masking the real IP address of a device, making it difficult for hackers to track and identify the location of the device. This type of software is commonly used by businesses, individuals, and healthcare organizations to protect sensitive data and prevent cyber attacks.
Types of Threats that IP Address Security Software Can Help Protect Against
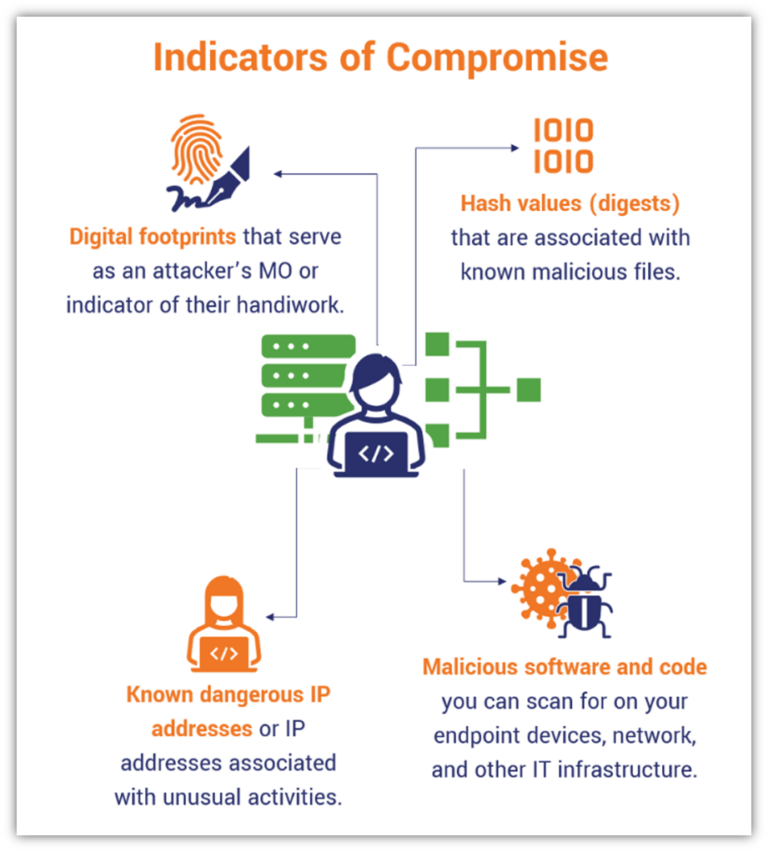
IP address security software can help protect against a variety of cyber threats, including:
- Unauthorized access
- IP spoofing
- Man-in-the-middle (MITM) attacks
- DDoS attacks
- Ransomware attacks
- Malware attacks
- Phishing attacks
Top IP Address Security Software Solutions
There are many top-rated IP address security software solutions in the market, including:
Features to Look for in IP Address Security Software
When selecting an IP address security software solution, there are several features to look for, including:
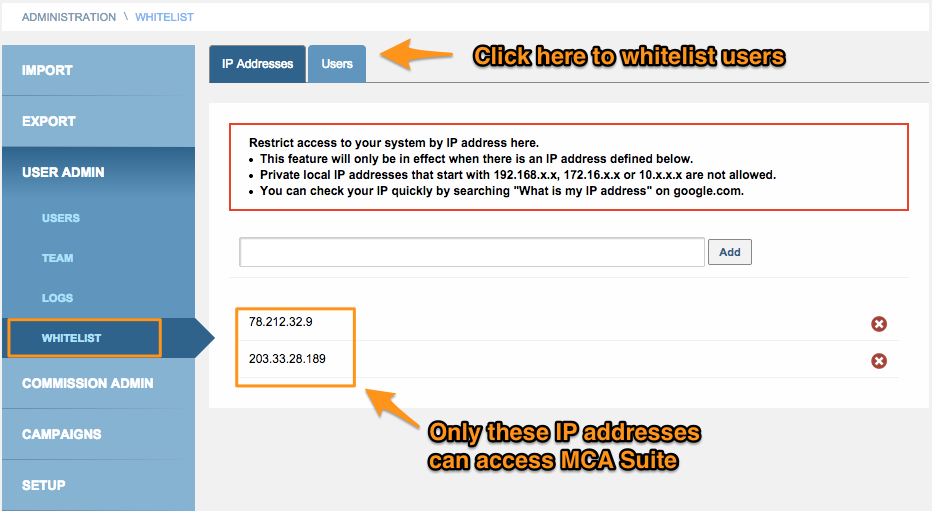
- IP address masking and rotation li>IP address blocking and filtering
- Real-time monitoring and threat detection
- Compliance with industry regulations and standards
- Easy integration with existing security infrastructure
- Scalability and flexibility to meet the needs of growing businesses
Conclusion
IP address security software is a critical component of any cybersecurity strategy, helping to protect businesses and individuals from a wide range of cyber threats. By selecting the right solution and configuring it correctly, organizations can ensure the security and integrity of their online identity and sensitive data. In this article, we have explored the importance of IP address security software, the types of threats that it can help protect against, and the top solutions in the market. We have also highlighted the key features to look for when selecting an IP address security software solution. By following these guidelines, organizations can make informed decisions about their cybersecurity strategy and ensure the long-term security and integrity of their online identity.
(IP Address Security Software) Benefits
Increased Security
IP address security software provides an additional layer of security to protect against unauthorized access, hacking, and other types of cyber threats.
Improved Compliance
IP address security software helps organizations meet industry regulations and standards, reducing the risk of fines and reputational damage.
Reduced Threats
IP address security software reduces the threat of cyber attacks, minimizing the risk of data breaches and other types of security incidents.
Enhanced Network Performance
IP address security software can also improve network performance by allowing organizations to segment their network and isolate sensitive systems.
Common Applications
Business and Enterprises
IP address security software is widely used by businesses and enterprises to protect their online identity and sensitive data.
Healthcare Organizations
IP address security software is also used by healthcare organizations to protect patient data and prevent cyber attacks.
Financial Institutions
IP address security software is widely used by financial institutions to protect customer data and prevent cyber attacks.
IP Address Security Software
IP address security software is a type of cybersecurity software that helps protect IP addresses from unauthorized access, hacking, and other types of cyber threats. It works by masking the real IP address of a device, making it difficult for hackers to track and identify the location of the device. By selecting the right solution and configuring it correctly, organizations can ensure the security and integrity of their online identity and sensitive data.