Ensuring Online Data Safety: Best Practices for a Secure Digital Life
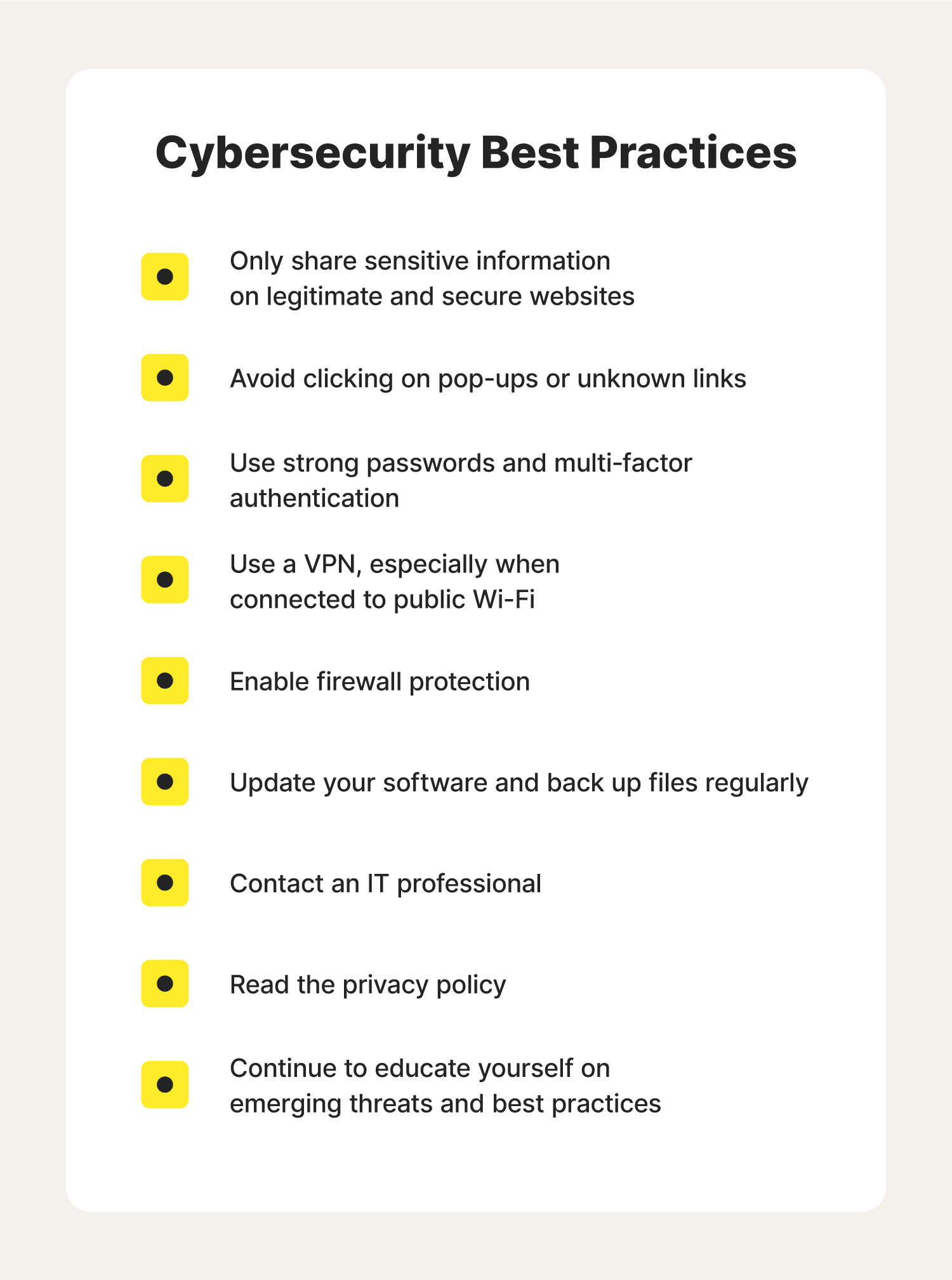
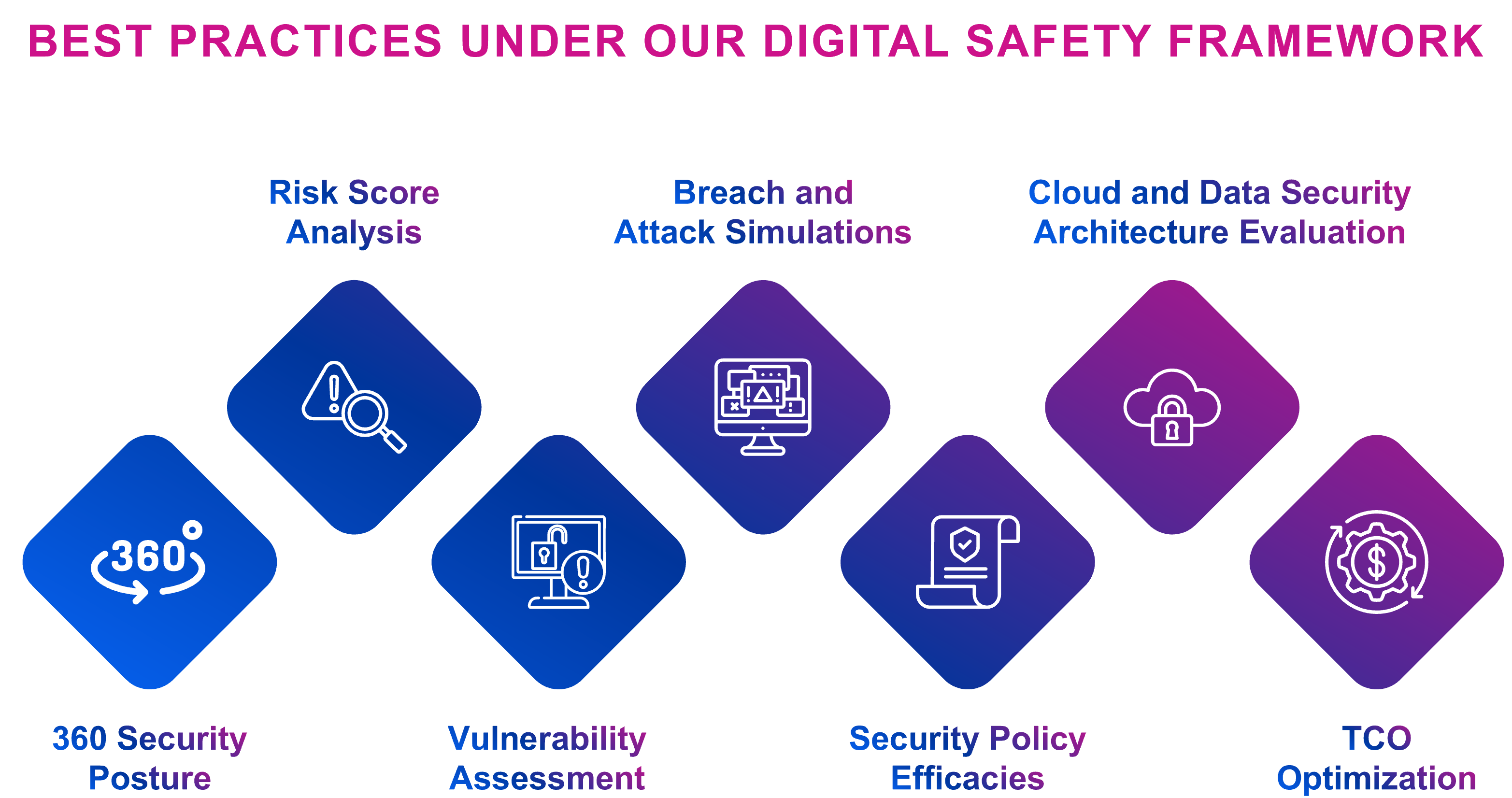
In today's digital world, online data safety has become a pressing concern for individuals and organizations alike. With the rise of cyber threats and data breaches, it's essential to adopt robust best practices to safeguard valuable data. This article will delve into the world of online data safety, exploring the top best practices to mitigate risks, prevent breaches, and secure sensitive information.Classify Data by Sensitivity: A Key Online Data Safety Best Practice
One of the most critical online data safety best practices is to classify data by sensitivity. This involves categorizing data into three levels of sensitivity: public, private, and confidential. Public data includes general information that can be shared with anyone, while private data includes sensitive information that requires protection, such as financial information or personal details. Confidential data includes highly sensitive information that requires strict protection, such as intellectual property or national security. By classifying data by sensitivity, organizations and individuals can implement targeted security measures to safeguard sensitive information, reducing the risk of data breaches and cyber attacks.Enforce Least Privilege: A Critical Online Data Safety Best Practice
Enforcing least privilege is another crucial online data safety best practice. This involves granting users the minimum level of access required to perform their job functions, reducing the risk of unauthorized access to sensitive data. By limiting user privileges, organizations can prevent data breaches caused by insider threats or misconfigured systems. To enforce least privilege, organizations can implement role-based access control (RBAC), which assigns users specific roles based on their job functions, rather than granting them blanket access to sensitive data.Secure Data at Rest: A Foundational Online Data Safety Best Practice








-A4.jpg)